Ankit kumar
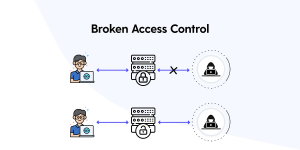
I am a cybersecurity professional specializing in penetration testing (VAPT), network security, and ethical hacking. With a passion for solving complex security challenges, I actively engage in Capture the Flag (CTF) competitions and share detailed walkthroughs to help others in the cybersecurity community. My goal is to identify vulnerabilities and strengthen defenses to create safer digital environments.
41 posts